CyAmast
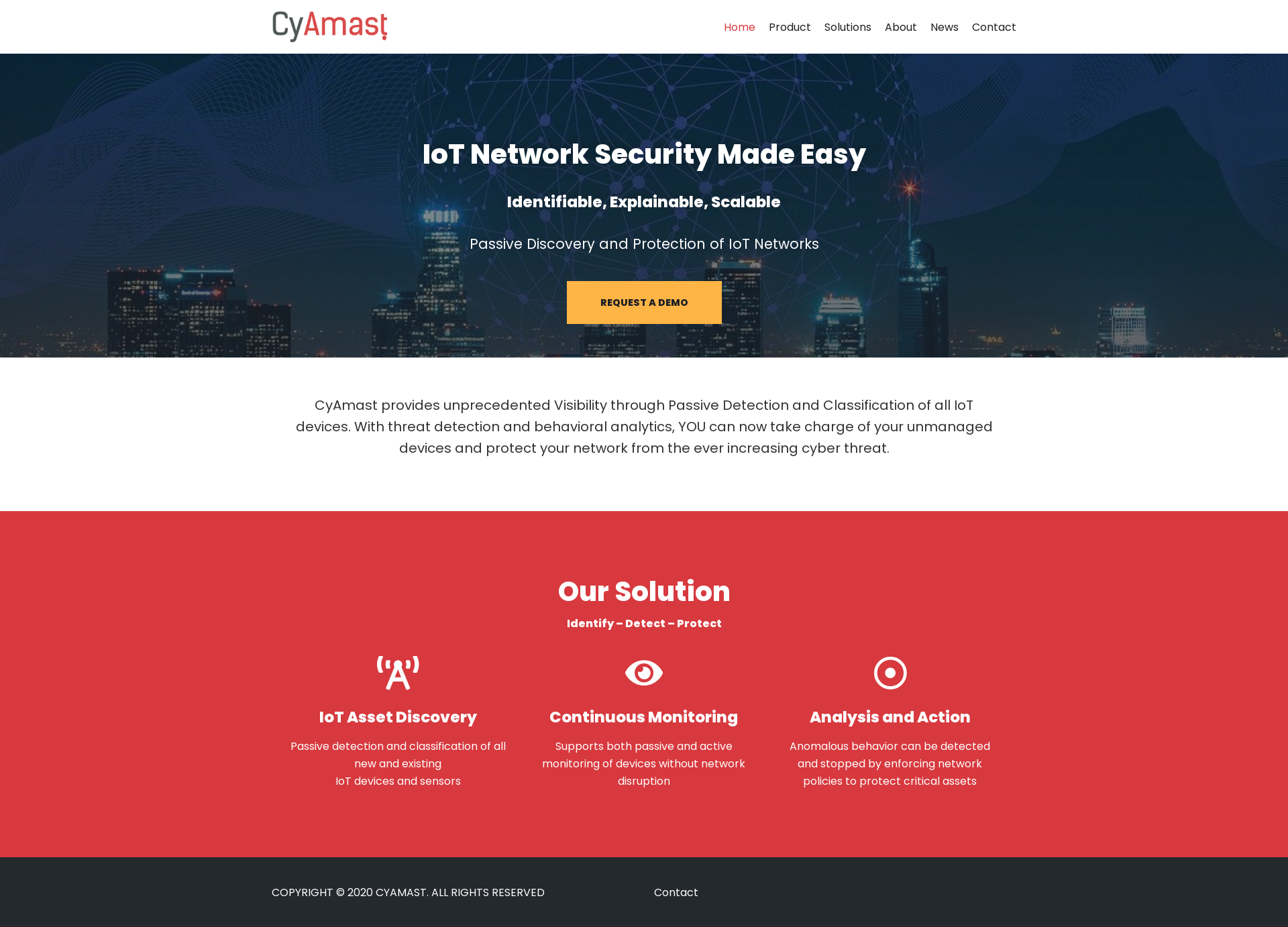
IoT Network Security Made EasyCyAmast
CyAmast provides unprecedented Visibility through Passive Detection and Classification of all IoT devices. With threat detection and behavioral analytics, YOU can now take charge of your unmanaged devices and protect your network from the ever increasing cyber threat.
Images
Blog Posts
23rd April, 2023
Asset Deployment and the Changing Face of Mining
As an industry, mining has always been slow to adopt new ideas due to the enormous upfront investmen...
19th October, 2021
How The Retail Sector is Using IoT
Using IoT technology, retailers can better serve their customers, save expenses, increase revenue, a...
19th October, 2021
How The Retail Sector is Using Digital Assets
Using IoT technology, retailers can better serve their customers, save expenses, increase revenue, a...
5th October, 2021
Telecommunications Deployments of IoT
The telecommunications industry is the unsung hero of the technology revolution, and it's the foiund...
5th October, 2021
Telecommunications Asset Deployments
The telecommunications industry is the unsung hero of the technology revolution, and it's the foiund...
10th September, 2021
How is the Hospitality Industry Leveraging IoT?
The future of hospitality will be powered by IoT. How is the industry already beginning to adopt thi...
10th September, 2021
How is the Hospitality Industry Leveraging IoT?
The future of hospitality will be powered by IoT. How is the industry already beginning to adopt thi...
3rd September, 2021
Data Centres and IoT
Data centres are the hubs for our modern existance. They are transforming how IoT is used, and IoT i...
3rd September, 2021
Data Centres and Digital Assets
Data centres are the hubs for our modern existance. They are transforming how IoT is used, and IoT i...
20th August, 2021
IoT Deployments and the Changing Face of Mining
Mining is changing with the adoption of IoT. How can it make the most of becoming 'smart' and avoid ...